Evidence of Internet Censorship during Catalonia's Independence Referendum
Tord Lundström (Virtual Road), Maria Xynou (OONI)
2017-10-03
Translation(s):
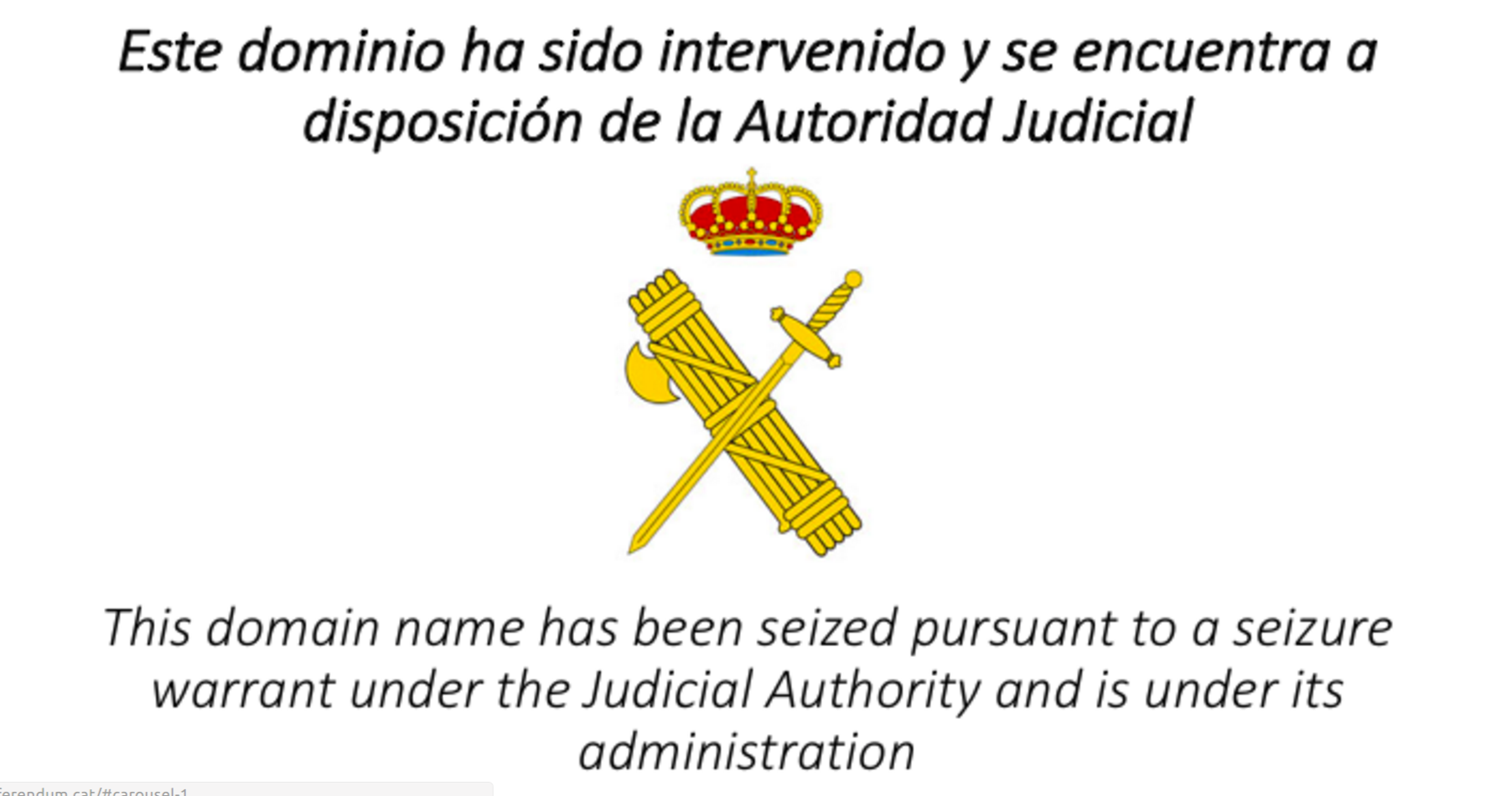
Image: Catalan Independence Referendum site seized
Two days ago, Catalonia held a
referendum seeking
independence from Spain. As the world awaits to see what happens next,
we publish this post to share
evidence of recent
censorship events that occurred during and leading up to the referendum.
We confirm the blocking of at least 25 sites related to the Catalan
referendum by means of DNS tampering and HTTP blocking, based on
OONI Probe network measurements
collected from three local networks. OONI data shows that these sites
were blocked every day from (at least) 25th September 2017 (when the
testing started) leading up to the referendum day, on 1st October 2017.
Catalan Independence Referendum
Catalans have their own language and cultural identity, despite being
part of Spain. Their president Carles Puigdemont
argues
that they have a moral, cultural, economic, and political right to
self-determination. In recent years, the Catalan independence movement
has strengthened, particularly in light of Spain’s economic crisis. Many
independence supporters
argue
that Catalonia has long been oppressed under the Spanish central
government that does not acknowledge their “right to decide”.
Catalonia has seeked more autonomy and independence from Spain in
various occasions. In 2006, Catalonia held a referendum amending the Statute of Autonomy of Catalonia,
expanding its regional government’s authority. But four years later,
Spain’s Constitutional Court reviewed the law upon request from the
Spanish government led by the Popular Party (PP), re-writing and
dictating the interpretation of many of its articles, and leading to a
massive demonstration in
Barcelona.
On 9th November 2014 (9N), Catalonia held a non-binding
self-determination referendum, where
voters were asked whether they wanted Catalonia to be a state and
whether they wanted that state to be independent. Even though 80% of ballots were cast in favour of both
questions (though the voter turnout was quite low), Spain’s
Constitutional Court ruled the referendum “unconstitutional and null.”
Such events paved the way for Catalonia’s latest referendum, but this
time the Spanish government showed less tolerance.
Leading up to the referendum, Spanish police raided Catalan regional government offices and arrested senior officials.
They also raided the offices of the .cat internet registry.
Domains associated to the referendum, like
referendum.cat and ref1oct.cat, have been seized. But censorship
events were not limited to .cat domains. Many in Catalonia
reported
that access to various other domains (mirrors) related to the Catalan
referendum were being blocked as well.
To ensure that voters could participate even if their appointed voting
stations were shut down
by the police, the Catalan government announced the “open census” in the
morning of the referendum (1-O). Voters were offered the opportunity to
choose any voting station in the country. However, the central system
that validated that the voters were in the census was taken down by Amazon
during the first hours of the day. Google was also previously ordered to take down a voting app
that provides information about the polling stations for the Catalan
independence referendum.
Despite all the attempts to block the process, alternative servers to
count votes were deployed and the referendum (1-O) was held last Sunday.
Locals reported that they had difficulty accessing the internet at the
polling stations, but we don’t have data to confirm whether throttling
or an internet blackout took place.
According to Catalan officials, 90% of more than 2.2 million ballots were cast in favour of independence.
However, the referendum was far from peaceful, as heavy police violence
resulted in hundreds of voters injured. Today,
thousands are protesting
against Spanish police violence on the streets of Barcelona, in response
to the crackdown during the referendum.
Catalonia’s president asked the European Commission to encourage international mediation
with Spain over the region’s independence. Madrid maintains that the
referendum was
illegal
and its outcome therefore null. Spain is currently experiencing one of its biggest political crises in decades. Even
Catalan society is quite
divided
on the question of independence.
We recognize the sensitivity of the current political situation. Through
empirical data collected by
OONI Probe community members
in Spain and Catalonia, we aim to support public debate.
Blocking of Catalan referendum sites
To collect evidence showing whether and how sites associated to the
Catalan referendum were blocked, OONI Probe tests were run in Catalonia over
the last week. OONI Probe is free and open software that anyone can
run to measure the blocking of
websites. All network measurement data collected by OONI Probe is
automatically published
to increase transparency of internet censorship worldwide.
OONI data confirms
that, as of 25th September 2017 (when OONI Probe testing started), local
ISPs have been blocking access to (at least) 25 Catalan referendum sites
and continued to enforce the blocks on the referendum day.
The table below links to network measurements collected from three local
ISPs and shows how and which sites were blocked on 1st October 2017,
when the Catalan independence referendum was held.
Many of the blocked domains (such as referendum.lol and
referendum.ninja) in the table above are mirrors of referendum.cat,
which was
seized
more than a week ago. The mirrors of blocked websites have been
run by volunteers using other top level domains (such as as .ninja .lol,
and .party).
OONI data shows
that these mirrors were blocked by means of DNS tampering and through
block pages served by HTTP transparent proxies. Daniel Morales, a
freedom of expression activist who worked on the scripts to mirror the
blocked sites, was called to appear in court on 22nd September
and accused of being supported by Russian hackers
by El Pais, one of Spain’s largest media outlets.
France Telecom Espanya (AS12479) and Euskaltel (AS12338) blocked access
to sites by means of DNS tampering, while Telefonica de Espanya (AS3352)
served block pages through the use of HTTP transparent proxies. It’s
worth noting that France Telecom Espanya (AS12479) and Euskaltel
(AS12338) didn’t block certain .cat domains (referendum.cat and
ref1oct.cat), likely because those sites had already been seized.
Telefonica de Espanya (AS3352), on the other hand, reinforced the
censorship by serving block pages for seized domains as well.
OONI data shows the blocking of the above sites leading up to the
referendum, between 25th September 2017 to 1st October 2017. Such data
can be accessed through the following steps:
Access the Spanish page of OONI Explorer
Click “Filter Results”
Add one of the domains (from the table above) in the “Test Input” section
Optional: Filter the measurements by date through the “Date Range” section
Click “Apply Filter”
Click on one of the filtered measurements
Scroll to the end of the measurement page
Click “Object” to view the network measurement data
Alternatively, the data can be download and analyzed through json files
included in OONI’s API.
Other measurements collected from sensors that provide DNS historical
values show that referendum.cat was redirected to the domain
paginaintervenida.edgesuite.net hosted by Akamai on 13th September.
2017-09-13 16:30:46 -0000 IN CNAME paginaintervenida.edgesuite.net.
As of 3rd October 2017, the following domain names are redirected to
paginaintervenida.edgesuite.net:
iolin.cat
Ref1oct.cat
Webdelsi.cat
Empaperem.cat
Garanties.cat
Joconvoco.cat
Vullvotar.cat
Prenpartit.cat
Referendum.cat
Votaras1-o.cat
7democracia.cat
Sorayasaenz.cat
Marianorajoy.cat
Referendumcat.cat
1octreferendum.cat
Holademocracia.cat
Referendumoct1.cat
Cridademocracia.cat
Referendumoctubre1.cat
All the .cat domains have been taken down as the result of the court order
that Fundacio .cat received on 15th September from the Tribunal
Superior de Justicia de Cataluña (TSJC). The director of research and
information of the organization that runs the Catalan top level domain
.cat, Pep Oliver, was detained on 20th September and retained under
custody for 60 hours.
Conclusion
In summary, three main techniques have been used to censor Catalan
referendum sites:
DNS tampering
The DNS resolvers of the operators are configured to return bogus DNS
responses to block the domain names. This technique can be applied for
any domain but can be bypassed by changing the DNS resolvers of the
devices (by using Google 8.8.8.8, for example, instead of the operator
DNS server).
OONI data shows
that France Telecom Espanya (AS12479) and Euskaltel (AS12338) adopted
this technique to block sites related to the Catalan referendum.
HTTP(S) blocking
This technique inspects, intercepts and alters web traffic so that HTTP
and/or HTTPS requests to URLs are replaced by a new page (“block page”)
indicating that they have been blocked.
OONI data shows
that Telefonica de Espanya (AS3352) adopted this technique to block
sites related to the Catalan referendum. Traffic recordings and analysis
of the blocking indicate that Telefonica might be using Israeli
technology from Allot Communications.
.CAT domain seizure
Once Fundacio .CAT implemented the court order, the domains have been
redirected by means of DNS to the domain paginaintervenida.edgesuite.net
hosted on Akamai. Many .cat domains though were also blocked by means of
DNS tampering and HTTP blocking.
The future of Catalonia remains quite unclear. What is clear is that
it’s important to keep those in power to account, even in “Western
democracies”. One way of doing so is by measuring networks and increasing
transparency of information controls.
Evidence is necessary for informed public debate.
Update (2017-10-05 16:30 UTC): As community members in Spain and Catalonia come across more blocked sites, they are added to this list here.
Update (2017-10-04 16:00 UTC): Qurium / Virtual Road have published data showing the mechanisms used to block websites associated to the referendum of 1-O of Catalonia. View their findings here.
Update (2017-10-03 20:38 UTC): Courtesy of our friends from Security Without
Borders,
you can run OONI Probe to test
Catalan websites for censorship by clicking on the “Run OONI” button below:
Test Catalan referendum sites